Providers
Authentication Providers in NextAuth.js are how you define services can be used to sign in.
NextAuth.js is designed to work with any OAuth service, it supports OAuth 1.0, 1.0A and 2.0 and has built-in support for many popular OAuth sign-in services. It also supports email / passwordless authentication.
Sign in with OAuth
Built-in providers
- Apple
- Auth0
- Battle.net
- Box
- Amazon Cognito
- Discord
- GitHub
- GitLab
- IdentityServer4
- Mixer
- Okta
- Slack
- Spotify
- Twitch
- Yandex
Using a built-in provider
Register your application at the developer portal of your provider. There are links above to the developer docs for most supported providers with details on how to register your application.
The redirect URI should follow this format:
[origin]/api/auth/callback/[provider]For example, Twitter on
localhostthis would be:http://localhost:3000/api/auth/callback/twitterCreate a
.envfile at the root of your project and add the client ID and client secret. For Twitter this would be:TWITTER_ID=YOUR_TWITTER_CLIENT_IDTWITTER_SECRET=YOUR_TWITTER_CLIENT_SECRETNow you can add the provider settings to the NextAuth options object. You can add as many OAuth providers as you like, as you can see
providersis an array.pages/api/auth/[...nextauth].js...providers: [Providers.Twitter({clientId: process.env.TWITTER_ID,clientSecret: process.env.TWITTER_SECRET})],...Once a provider has been setup, you can sign in at the following URL:
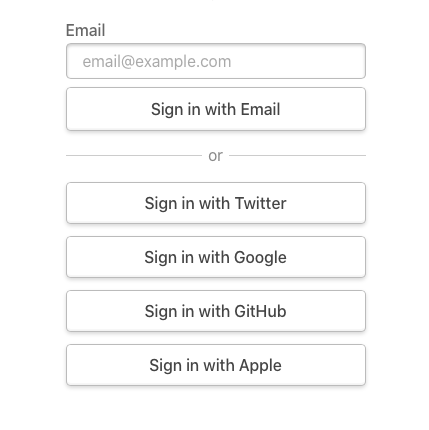
[origin]/api/auth/signin. This is an unbranded auto-generated page with all the configured providers.
tip
If you want to create a custom sign in link you can link to /api/auth/signin/[provider] which will sign in the user in directly with that provider.
Using a custom provider
You can use an OAuth provider that isn't built-in by using a custom object.
As an example of what this looks like, this is the the provider object returned for the Google provider:
You can replace all the options in this JSON object with the ones from your custom provider – be sure to give it a unique ID and specify the correct OAuth version - and add it to the providers option:
Options
| Name | Description | Required |
|---|---|---|
| id | An unique ID for your custom provider | Yes |
| name | An unique name for your custom provider | Yes |
| type | Type of provider, in this case it should be oauth | Yes |
| version | OAuth version. | Yes |
| scope | OAuth access scopes | No |
| params | Additional authorization URL parameters | No |
| accessTokenUrl | Endpoint to retrieve an access token | Yes |
| requestTokenUrl | Endpoint to retrieve a request token | No |
| authorizationUrl | Endpoint to request authorization from the user | Yes |
| profileUrl | Endpoint to retrieve the user's profile | No |
| profile | An object with the user's info | No |
| clientId | Client ID of the OAuth provider | Yes |
| clientSecret | Client Secret of the OAuth provider | No |
| idToken | Set to true for services that use ID Tokens (e.g. OpenID) | No |
note
Feel free to open a PR for your custom configuration if you've created one for a provider that others may be interested in so we can add it to the list of built-in OAuth providers!
Sign in with Email
The Email provider uses email to send "magic links" that can be used sign in, you will likely have seen them before if you have used software like Slack.
Adding support for signing in via email in addition to one or more OAuth services provides a way for users to sign in if they lose access to their OAuth account (e.g. if it is locked or deleted).
Configuration is similar to other providers, but the options are different:
See the Email provider documentation for more information on how to configure email sign in.
note
The email provider requires a database, it cannot be used without one.
Sign in with Credentials
The Credentials provider allows you to handle signing in with arbitrary credentials, such as a username and password, two factor authentication or hardware device (e.g. YubiKey U2F / FIDO).
It is intended to support use cases where you have an existing system you need to authenticate users against.
See the Credentials provider documentation for more information.
note
The Credentials provider can only be used if JSON Web Tokens are enabled for sessions. Users authenticated with the Credentials provider are not persisted in the database.